About 75% of American parents post pictures of their children on Facebook and other social media sites. Approximately 80% of all Facebook users have “connections” to people whom they have never actually met. You do the math. That means countless kids’ activities, schools, sports teams, locations, ages, genders, and even names are available to strangers. These same strangers can dive much deeper into a person’s “digital footprint” to learn A LOT more about the individuals, their families, their finances, their politics, and their careers.
A digital footprint, also known as a digital trail or digital exhaust, is the collection of information that a person leaves behind as they engage in various online activities. This footprint is created by an individual’s interactions with the internet, including websites, search engines, social media, and online services. It includes the active information that is willingly shared as well as the passive data that is collected behind the scenes.
A digital footprint can have both positive and negative consequences. On the positive side, it can help connect with other users, access personalized content and services, and build a digital identity. On the other hand, it also comes with privacy concerns since the data can be used for targeted advertising, identity theft, or other malicious purposes. Furthermore, this information is frequently sold or shared with data brokers.
Components Of A Digital Footprint:
A digital footprint can come from many different sources. Some of the more common components are listed below:
- Social Media Activity: This is the most notorious source for information. It includes social media posts, comments, likes, and shares from Facebook, Snapchat, X (Twitter), LinkedIn, and Instagram. These platforms often store a history of actions too.
- Online Accounts and Registrations: When a user creates accounts on websites, forums, or online services, that information becomes part of a digital footprint. This could include the user’s name, email address, birthday, and more.
- Search History: Search engine queries for Google or Bing are recorded and can be used to build a profile of a user’s interests and preferences.
- Browsing History: The websites that a user visits, the pages that are viewed, and the time spent on them create part of a digital footprint. This data is often tracked through browser cookies, and then it can be used for targeted advertising and analytics.
- Location Data: Many devices and applications track users’ locations, leaving a clear trail of where they have been. This information can be used to create a map of someone’s movements.
- Online Shopping: Information related to online shopping habits, including what and where a person buys, becomes part of the digital footprint.
- Brick and Mortar Stores: Warranty cards and loyalty programs are also components of a digital footprint.
- Home Purchases: The purchase date and price, mortgage, title, and sometimes even insurance all become public records.
- Email Communications: The content of emails, as well as the metadata associated with them, can all contribute to an individual’s digital footprint.
- Online Posts and Content Creation (like this!): Blogs, forums, comments on articles, and other published online content also become part of the digital footprint.
- Device Information: The physical devices that are used to access the internet (e.g. smartphones, tablets, computers) all have unique identifiers that can be used to track the users’ digital activities.
- Apps and Services: Usage of various applications and online services like fitness trackers and productivity tools can be logged and used to create a profile of a user’s behavior.
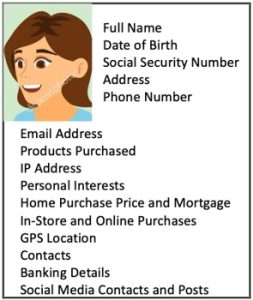
- The Jackpot – Credit Report Header Data: Consumers will volunteer credit report data that typically contains their full name, date of birth, social security number, current and prior addresses, and telephone number. This information is NOT protected by the Fair Credit Reporting Act (FCRA), and it can be legally sold to third parties.
What They Have On You: It is essential that you are aware of your digital footprint. Many people can expect that profiles like the one below exist in cyberspace – there may also be similar footprints for family members, including children. These can be bought, sold, or even modified without your permission of knowledge.
Tools such as VPNs or ad-blockers can help enhance your online privacy, but they are far from foolproof.
Appendix – Opting Out: There are several steps that you can take to manage and protect your online presence. It should be mentioned that there are a dozen different services that will clean up your digital footprint for you, generally for a monthly subscription fee. These get very mixed reviews, so please research them before committing. Also, ironically, these services generally need to collect a user’s personal information before they can sanitize their cyber records.
We are going to pursue the DIY approach. For starters, be mindful of what you share online, and periodically delete unnecessary information. Also, stay away from all online polls, questionnaires, and surveys – they only exist to mine your data. You can adjust the privacy settings in most applications, thereby limiting the information that the apps collect and share. However, there are a lot of applications out there, and this can be a long and laborious process. With that in mind, we will tackle a few of them at a time over the next several weeks.
For this issue, let’s start with the most scandalous site: Facebook. It is important to understand that Facebook’s business model consists of selling targeted advertising, based on the personal information that you share online. This means that their whole system is designed to collect as much information about you, your family, and your Facebook friends as possible. However, the following procedures can help reduce the personal risk associated with using their services (please scrutinize these settings on your kids’ accounts too):
1. General Information
a. Use a separate email address and phone number for your Facebook account. These should not be linked to any other accounts or applications. (Note – you can get a free “soft phone” application and number if necessary.)
b. Facebook has its own Security Checkup process – this is very helpful.
2. Privacy Settings
a. Select your audience. This allows you to decide who sees whatever you share. Use the “Custom” option to create very specific filters. But keep in mind that when you post something to another user’s Timeline, that person now controls the viewership. Also, anyone who is tagged in a post may see it, along with their friends.
b. Select the option that lets you review and approve (or reject) all posts that you are tagged in before they appear on your Timeline.
c. Reject Search Engine Visibility – this will prevent information in your profile from appearing in public search engine results. (Keep in mind that this doesn’t apply to any public groups or forums that you may have joined.)
3. Location Settings
a. These are enabled by default (except for minors). These are only applicable to iOS and Android devices. Use your phone’s or tablet’s “setup” functions to disable location settings for Facebook.
4. Advertising
a. Go to Account Settings Ad Preferences.
i. Advertisers: This will show you how Facebook already used your information for advertising purposes; you can’t change this, but it is useful information.
ii. Your Information: This data indicates how Facebook serves advertisers; it does not affect your profile. Review the options and enable/disable buttons as needed.
iii. Ad Settings: Disable all!
5. Contact Deletion Tool
a. This will delete your phone number, mobile number, and email from Facebook’s/Meta’s database.
6. Facebook Community
a. Friend Requests should only be used to connect with people whom you personally know. Friends-of-friends should always be suspect. Also be leery of possible clones of some of your contacts. Spoofed contacts are a common attack vector.
b. Do not use your full name.
c. Do not be afraid to unfriend or block someone, especially if you don’t know them personally.
d. Do not hesitate to report someone who shares inappropriate information.
7. Facebook Messenger
a. Disable Facebook Messenger’s ability to automatically sync all of your contacts. People Upload Contacts off. (You may need to delete all of your contacts first, if they have already been uploaded.)
b. Use encrypted “secret” conversations for privacy.
c. Clear your search history regularly.
d. Remove sent messages periodically.
Watch this space for more “Opt Out” instructions over the next few weeks.